An extra layer of security for your site
The easy way to completely hide your WordPress, plugins and themes
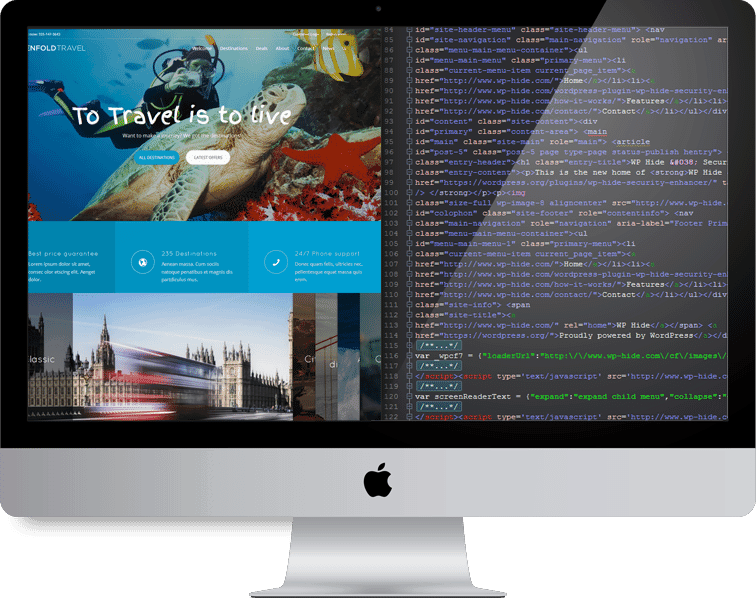
WP-Hide Explained
Over 99,99% of sites hacks are focused attacks on specific plugins and themes vulnerabilities. A huge improvement over Site Security since hackers web scanners will not find any WordPress traces on your site. Since no WordPress plugins and themes are found anymore, no hack occur even if the site contains exploitable code.
Provides a clean method for removing any WordPress fingerprints including themes and plugins.
No negative impact on SEO at all! Used wisely, specific SEO aspects can be improved.
WP HIDE PRO now available!
Plugin Features

No files and directories changes!

100% compatible with other Plugins & Themes

WordPress MultiSite Compatible

Theme Masking

Compatible with any host / server

Nginx Compatible

Custom login URL

HTML clean-up

Individual Plugin URL customization

Change WP Ajax calls
Firewall
White label themes/plugins
Very popular plugins (including JetPack, bbPress, Gravity Forms, WordPress SEO) were found vulnerable to XSS attacks. This can happen again for other plugins too.
Do not jeopardy your site security, hackers never sleep
Check for yourself !
No WordPress detectors can see any detail about Our Site, no plugins info, no theme specifications, no WordPress at all !!
Prevention is better than cure
Start protecting your Business today!
Why use?
There’s no doubt that WordPress is by far the most popular Content Management System available. The platform growth has seen an unprecedented increase in the past few years. It is still expanding at a rate of a few percent per year and beat all records. Statistically, it’s being used by 60% of Top 100 blogs, deployed for over 90 million active sites, more than 40 million terms searches per month.
With over 30% of the world’s websites running over WordPress, the day when it will cross all barriers to touch the majority in the world, is near the corner. But all this attention comes with a price! Hackers keep their keen eye on the WordPress platform.
Security breachs in themes and plugins represent more than 98% of all successful WordPress hacks. If a single vulnerability is found within a WordPress install, millions of website become easy targets. If you use WordPress, this is a clear threat to your business. New security issues are reported every day, see only a fraction reported at Sucuri Website.


Perfect solution!
WP Hide & Security Enhancer plugin for WordPress makes it easy for sites administrators to completely hide their CMS identity. The formula is simple, it hides WordPress fingerprints such as resource URLs (plugins, theme, core files), login url, block REST and XMLRPC services etc, This makes it completely blind for boots attacks, that try to identify specific plugins and themes and their vulnerabilities.
The technical term is “Security by Obscurity”. In laymen terms, “If you cannot see and understand, how can you hack it?”
Hackers use bots and automated systems to find loopholes in specific WordPress versions. With WP Hide PRO active, the automated systems/bots will be useless as they won’t be able to see any WordPress at all, They can't get the most basic information about the platform being used.


